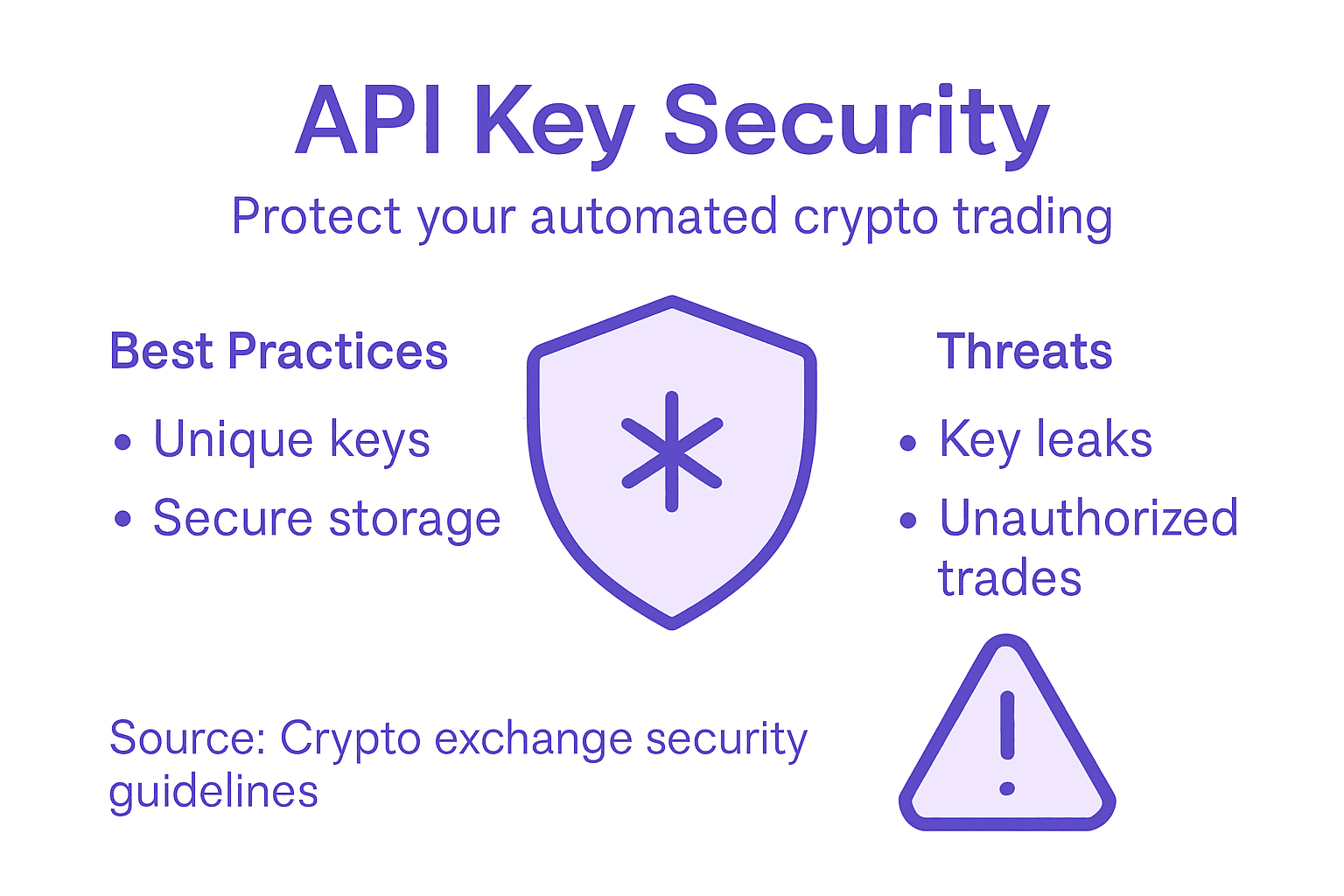
What Is API Key Security in Automated Crypto Trading
What Is API Key Security in Automated Crypto Trading

A single leaked API key can transform a thriving trading strategy into a costly mess. Automated cryptocurrency traders know the stakes are high when keys unlock not just their exchange accounts, but their entire operation. For busy professionals and algorithmic trading enthusiasts, understanding the core principles of API key security is essential to protect capital, minimize risk, and ensure seamless automation. This guide reveals how unique, random keys, strict permission controls, and encrypted transmission work together to safeguard your trading—before disaster strikes.
Key Takeaways
| Point | Details |
|---|---|
| API Key Security is Critical | A compromised API key can lead to unauthorized access to your trading operations and financial losses. |
| Use Unique and Random Keys | API keys should be uniquely generated and not reused across exchanges to prevent brute-force attacks. |
| Implement Least Privilege Access | Limit API key permissions to necessary tasks to reduce potential damage if a key is compromised. |
| Regular Monitoring and Rotation | Regularly audit and rotate API keys to detect unauthorized access and minimize security risks. |
Core Principles of API Key Security
API key security forms the foundation of safe automated trading. Without proper protection, your keys become a direct path to unauthorized access of your exchange accounts and funds.

Think of your API key like a password—except worse. A compromised password might expose your account. A compromised API key exposes your entire trading operation, positions, and capital.
Generation and Randomness
Every API key must be unique and randomly generated. Unique, random API keys prevent attackers from guessing or predicting valid credentials through pattern analysis or brute force attacks.
Exchanges should generate keys using cryptographically secure random number generators. Weak randomness creates exploitable patterns that sophisticated attackers can leverage.
When creating API keys for your bots, never reuse the same key across multiple exchanges or accounts. Each integration requires a fresh, unique credential.
Storage and Protection
How you store API keys determines whether they remain secret. Never hardcode keys into scripts, configuration files, or version control systems. A single developer mistake exposes credentials to anyone with repository access.
Secure storage practices include:
- Store keys in environment variables or secure configuration management systems
- Use encrypted vaults designed for credential storage
- Implement access controls limiting who can view stored keys
- Rotate keys periodically, especially after team changes
API keys should only be displayed once at creation. If you don’t save them immediately, you lose access and must generate new ones.
Principle of Least Privilege
Permission restrictions are fundamental to reducing damage from key compromise. Your automated trading bot doesn’t need every permission available.
Limit your API keys to exactly what your bot requires:
- Trading permissions only (not withdrawal rights)
- Specific trading pairs if the exchange allows
- Read-only access for market data endpoints
- Restricted access to account management functions
If an attacker obtains a key with limited permissions, their damage remains contained. A key with full account access invites complete account takeover.
Secure Transmission
Transmitting API keys requires HTTPS encryption, never plain HTTP. This prevents man-in-the-middle attacks where network traffic gets intercepted during transmission.
When protecting against API security risks, secure communication channels are non-negotiable. Your trading platform must enforce encrypted connections for all API communications.
Monitoring and Rotation
Regularly audit which keys exist and what permissions they hold. Remove unused keys immediately and rotate active keys on a defined schedule.
Monitor API usage patterns. Unusual activity—unexpected geographic locations, off-hours access, or unusual request volumes—signals potential compromise.
Pro tip: Set API key expiration dates automatically in your exchange settings, forcing regular rotation without manual intervention.
API Key Types and Permission Controls
Not all API keys serve the same purpose. Different key types handle different security requirements, and permission controls determine what each key can actually do once it’s authenticated.
Understanding these distinctions prevents over-privileging your automated trading setup. A key with excessive permissions becomes a larger target for attackers.
Key Types in Crypto Trading
API keys come in different varieties depending on how they authenticate and what they protect. The most common types for automated trading include read-only keys and trading keys.
Read-only keys access market data and account information without modifying anything. They pull price data, view your portfolio, and retrieve order history. Attackers with read-only credentials can observe your positions but cannot execute trades or withdraw funds.
Trading keys execute orders, manage positions, and modify open trades. These carry significantly more risk because compromise means unauthorized trading on your account.
Some exchanges offer withdrawal keys as a separate credential type. These control fund transfers only. The best practice isolates withdrawal permissions from trading permissions entirely.
Below is a concise comparison of API key types and their security implications in crypto trading:
| Key Type | Primary Use | Security Risk if Compromised | Example Restriction |
|---|---|---|---|
| Read-Only | Market data access | Exposure of strategy and history | No trading or withdrawals |
| Trading | Executing buy/sell orders | Unauthorized trades, losses | No withdrawal permissions |
| Withdrawal | Transferring funds | Direct asset theft | Separate from trading credentials |
Permission Granularity
Modern exchanges implement granular permission systems where you customize exactly what each key can do. This follows the principle of least privilege—giving keys only the minimum access required.
Typical permission categories include:
- Read account balances and open orders
- Place and cancel trades
- Modify order parameters
- View trading history
- Access withdrawal functions
- Manage API key settings
Your bot for grid trading should never have withdrawal permissions. Your key for market data collection should never have trading permissions. Segmenting responsibilities reduces fallout from individual key compromise.
Fine-grained permission controls enable defining specific access rights per key, preventing unnecessary privilege escalation when keys are compromised.
Exchange-Specific Implementation
While principles remain consistent, different exchanges implement permission controls differently. Some offer more granularity than others.
When setting up API key integration for trading automation, review your exchange’s specific documentation. Most major exchanges support:
- IP address whitelisting (restricting key use to specific locations)
- Rate limiting (capping requests per minute)
- Specific trading pair restrictions
- Timestamp validation windows
Restricting by IP address adds a physical security layer. If your key leaks, attackers cannot use it from unauthorized locations.
Multi-Key Strategy
Professional traders create separate keys for different functions. One key handles market data collection, another executes trades, and a third monitors performance.
This segmentation contains damage. If a data-collection key leaks, your trading remains protected. If a trading key becomes compromised, you rotate only that credential without disrupting monitoring or data access.
Pro tip: Create separate API keys for each distinct bot function, rotating them on different schedules so compromise of one key doesn’t require replacing your entire trading infrastructure at once.
How API Keys Enable Crypto Automation
API keys are the bridge between your trading strategy and actual execution. Without them, your bot remains disconnected from exchanges and cannot act on your behalf.
Think of an API key as a cryptographic credential that says “this request comes from an authenticated user.” The exchange trusts this credential and processes commands accordingly.
Authentication Without Human Intervention
Automated trading requires your bot to prove its identity to exchanges thousands of times per day. Manual login for each trade is impossible. API keys solve this by providing persistent authentication credentials that survive across multiple requests.
When your bot connects to an exchange, it sends the API key alongside every request. The exchange verifies the key matches a registered account and allows the operation to proceed. No human needs to approve each transaction.
Secure authentication for automated operations maintains the integrity of your trading system by ensuring only authorized bots execute trades on your account.
Real-Time Data Access
Your bot needs live market data to make decisions. API keys grant programmatic access to price feeds, order books, and account balances.
Without API keys, you would manually check prices and manually place orders. With them, your bot retrieves data and executes trades in milliseconds. This speed advantage matters significantly in volatile markets.
Data access happens continuously:
- Fetch current prices for decision-making
- Retrieve your account balance and open positions
- Monitor order fill status in real time
- Check trading history for strategy analysis
Order Execution at Scale
API keys enable bots to place, modify, and cancel orders automatically based on predefined logic. Your strategy becomes a series of programmatic instructions rather than manual tasks.
A grid trading strategy might place 100 orders across price levels. Doing this manually takes hours. Via API, your bot executes all orders in seconds, capturing opportunities before market conditions shift.
Execution speed creates compound advantages. Early entry on price moves, rapid response to volatility, and systematic rebalancing become possible only through API automation.
Request Signing and Authorization
Modern exchanges use cryptographic signatures to verify requests genuinely originate from your account. Your API secret combines with request data to generate a unique signature that proves authenticity.
This prevents man-in-the-middle attacks where intercepted credentials could be reused. Each request carries a timestamp-locked signature that expires quickly, adding another layer of protection.
API-based automation removes emotional decision-making and executes strategies with mechanical consistency, regardless of market conditions or time of day.
Multi-Exchange Coordination
Traders managing portfolios across multiple exchanges benefit from API keys enabling coordinated execution. One bot can monitor prices on Exchange A, execute on Exchange B, and rebalance on Exchange C simultaneously.
This coordination would be impossible manually. APIs make it routine.
Pro tip: Use separate API keys for each exchange and each bot function, allowing you to enable or disable specific automation without affecting your entire trading operation.
Risks of API Key Exposure and Misuse
A single leaked API key can unwind months of disciplined trading strategy in minutes. The damage extends beyond immediate financial loss to include account takeover, data theft, and operational disruption.
Understanding these risks shapes how you handle credentials and what safeguards you implement.
Unauthorized Trading and Fund Loss
When attackers obtain your API key, they gain the ability to execute trades on your behalf. Unlike a stolen password, they don’t need to change your account settings or withdraw funds to cause damage.
They can immediately:
- Place market orders at unfavorable prices
- Execute high-frequency trades that drain your balance through slippage
- Open leveraged positions that trigger liquidation
- Lock capital in illiquid altcoins
- Reverse your carefully positioned trades
An attacker with a trading key doesn’t need your withdrawal credentials. They wreak havoc through pure execution abuse. The exchange processes every order as legitimate because it carries valid authentication.
Resource Exhaustion and Denial of Service
Attackers exploiting exposed API keys can trigger massive request volumes that overwhelm exchange systems. This causes service degradation affecting legitimate traders, including you.
Resource exhaustion takes forms:
- Sending thousands of requests per second to drain rate limits
- Repeatedly placing and canceling orders to clog systems
- Querying market data excessively to trigger throttling
- Generating alerts and notifications that paralyze monitoring systems
Your bot gets blocked when rate limits hit zero, preventing you from executing trades during crucial market moves.
Data Exposure and Privacy Breach
Read-only API keys expose sensitive trading information. Attackers viewing your portfolio positions reveal your strategy, holdings, and trading history.
This information has value. Competitors learn your positions. Market manipulators understand your entry and exit points. Targeted attacks become possible when adversaries know your exact setup.
Broken Authorization and Privilege Escalation
Some exchanges implement authorization weakly across their API surface. A read-only key might access account settings it shouldn’t. A trading key might reach withdrawal functions.
Security misconfigurations in API implementations create pathways for attackers to exceed intended permissions. A leaked key becomes a skeleton key opening doors it was never meant to unlock.
Compromised API keys enable attackers to execute your strategy against you, using your own automation logic to maximize damage.
Persistent Access and Bot Hijacking
Attackers don’t immediately cash out stolen funds. Sophisticated attacks maintain quiet access, rotating through small transactions to avoid detection. Your bot continues running, but it’s serving two masters.
The attacker uses your bot’s speed and permissions to execute their strategy while you remain unaware. By the time you notice account drift, substantial damage has accumulated.
Learn how crypto trading bot security protects your operations by implementing detection and response mechanisms that catch unauthorized activity early.
Regulatory and Compliance Issues
Compromised accounts create compliance headaches. If unauthorized transactions trigger regulatory scrutiny, you face the burden of proving the activity wasn’t yours. Exchange freezes complicate recovery.
Pro tip: Enable email notifications for every API key creation and deletion, and monitor account activity logs daily to catch unauthorized access within hours rather than days.
Best Practices for Securing Trading API Keys
Securing API keys requires discipline across generation, storage, transmission, and lifecycle management. These practices separate traders who maintain account security from those who experience costly breaches.
Implementing these practices takes initial effort but compounds into long-term protection.
Generate High-Entropy Keys
API keys must be cryptographically random and non-guessable. Weak randomness creates exploitable patterns that attackers can predict through pattern analysis.
When generating keys through your exchange:
- Use the exchange’s native key generation system, not custom scripts
- Never manually create keys using simple patterns or sequences
- Regenerate keys if you suspect the randomness process is compromised
- Verify key length meets exchange security standards
High-entropy generation means the exchange uses industrial-strength random number generators. This prevents brute-force attacks where attackers guess valid credentials through trial and error.
Store Keys in Secure Vaults
Secure key storage and management practices protect credentials from theft and accidental exposure. Never store keys in plaintext files, environment variables, or version control repositories.
Secure storage options include:
- Hardware security modules (HSMs) for highest protection
- Encrypted password managers designed for credentials
- Environment variable services with access controls
- Encrypted databases with restricted permissions
Your trading bot should retrieve keys from secure storage at runtime, never embedding them in code. If code gets exposed, the keys remain protected.
Implement IP Whitelisting
IP whitelisting restricts key usage to specific locations. Even if attackers obtain your key, they cannot use it from unauthorized geographic regions or networks.
Configure your exchange to accept API requests only from:
- Your bot’s dedicated server or cloud instance
- Your office network
- Your home network (if trading from there)
Attackers in foreign countries with your key experience immediate rejection. The exchange logs failed authentication attempts, alerting you to compromise attempts.
Rotate Keys Regularly
Effective key rotation and revocation limits exposure window if compromise occurs. Create a rotation schedule independent of incidents.
Rotation frequency depends on risk tolerance:
- High-risk keys (trading execution): rotate monthly
- Medium-risk keys (data collection): rotate quarterly
- Low-risk keys (read-only monitoring): rotate semi-annually
After generating a replacement key, test it thoroughly before retiring the old one. Document rotation dates to catch keys that haven’t been rotated.
Monitor for Unauthorized Activity
Regularly review API usage logs for suspicious patterns. Unusual geographic access, off-hours requests, or abnormal request volumes signal compromise.
Set alerts for:
- New API key creation
- Keys accessing unexpected endpoints
- Request volumes exceeding normal patterns
- Failed authentication attempts
Catch compromise within hours, not weeks. Early detection prevents attackers from executing large unauthorized trades.
Multiple layers of defense—strong generation, secure storage, restricted access, and continuous monitoring—work together to prevent API key compromise from becoming a financial disaster.
Use Separate Keys for Different Functions
Never use a single master key for everything. Create separate credentials for trading execution, market data access, and account monitoring.
When managing trading bot security, segmentation contains damage from key compromise. Loss of a read-only data key doesn’t affect your trading capability.
Pro tip: Create a quarterly calendar reminder to rotate all API keys, and test new keys on small position sizes before decommissioning old ones to prevent service disruptions.
Here’s an overview of best practices and their benefits for securing trading API keys:
| Best Practice | Main Purpose | Impact if Neglected |
|---|---|---|
| High-entropy generation | Prevent brute-force guessing | Keys are easy to predict |
| Secure vault storage | Protect against unauthorized access | Accidental or malicious leak |
| IP whitelisting | Limit key use to trusted networks | Attackers can use keys globally |
| Regular rotation | Reduce exposure time if breached | Long-term silent compromises |
| Segmented permissions | Minimize damage from leaks | Full account takeovers possible |
Enhance Your Crypto Trading Security with Darkbot.io
The article highlights the critical challenges of protecting your API keys from unauthorized access and the risks of exposure in automated crypto trading. If you want to confidently automate your trading while embracing principles like least privilege permissions, secure storage, IP whitelisting, and regular key rotation, you need a platform that prioritizes these security essentials. Darkbot.io offers a robust, secure environment that seamlessly integrates your API keys across multiple exchanges with fine-grained permission controls and encrypted key management.
Take control of your automated trading strategy now with Darkbot.io. Experience dependable security combined with advanced AI-driven trading automation designed to protect your assets and optimize profits. Visit Darkbot.io to start automating securely today. Learn more about how our solution simplifies API key integration while maintaining stringent safety standards and crypto trading bot security that protects your investments from threats.
Frequently Asked Questions
What is the importance of API key security in automated crypto trading?
API key security is crucial as it protects your trading operations, positions, and capital from unauthorized access. A compromised API key can expose your entire trading setup, leading to significant financial losses.
How can I securely generate API keys for my trading bots?
When generating API keys, ensure they are unique and randomly generated using cryptographically secure methods. Avoid reusing keys across different exchanges and accounts to enhance security.
What are the best practices for storing API keys?
Store API keys securely using environment variables, encrypted vaults, or secure configuration management systems. Avoid hardcoding keys into scripts or configurations to prevent accidental exposure.
Why should I limit the permissions of my API keys?
Limiting API key permissions to only what is necessary (principle of least privilege) reduces the potential damage if a key gets compromised. For instance, using read-only access for data fetching prevents unauthorized trades or withdrawals.
Recommended
- API Key Integration: Simplifying Crypto Bot Automation
- Crypto Trading Bot Security: Protecting Profits and Data
- Cryptocurrency API Integration: Maximizing Automated Trading
- Crypto Trading Bot Terminology: Maximize Your Profits
- 7 Essential Security Awareness Trainings for Fintech Leaders
- Simple Tips for Website Security | Big Eye Deers Blog
Start trading on Darkbot with ease
Come and explore our crypto trading platform by connecting your free account!